Comments
- No comments found

With cyberattacks becoming more sophisticated, the defense against them should also advance.
To be a step ahead or in tandem with cyber threats or attacks, AI in cybersecurity could be the wall of defense.
Cybercriminals nowadays use various methods to hack into a system to alter, delete or intercept the data. In 2021, the breached reports reached up to 22 billion. With the world becoming more digitally connected and sensitive information being stored online, cybercriminals have an enormous area of opportunity to hack and extract data. To fight fire with fire, AI in cybersecurity is a solution that has endless benefits.
With the growing risk of cyber attacks being more elaborate and sophisticated than ever, the global AI cybersecurity market is projected to reach $133.8 billion by 2030. AI in cybersecurity can be the required intelligence to combat the technology used by hackers to breach the security systems that can destroy an organization.
Hackers find innovative ways to breach the security system of an organization. The organization, in turn, needs to be proactive in deploying the best possible defense against such breaches. Here are some of the ways AI doubles up as a weapon against hackers.
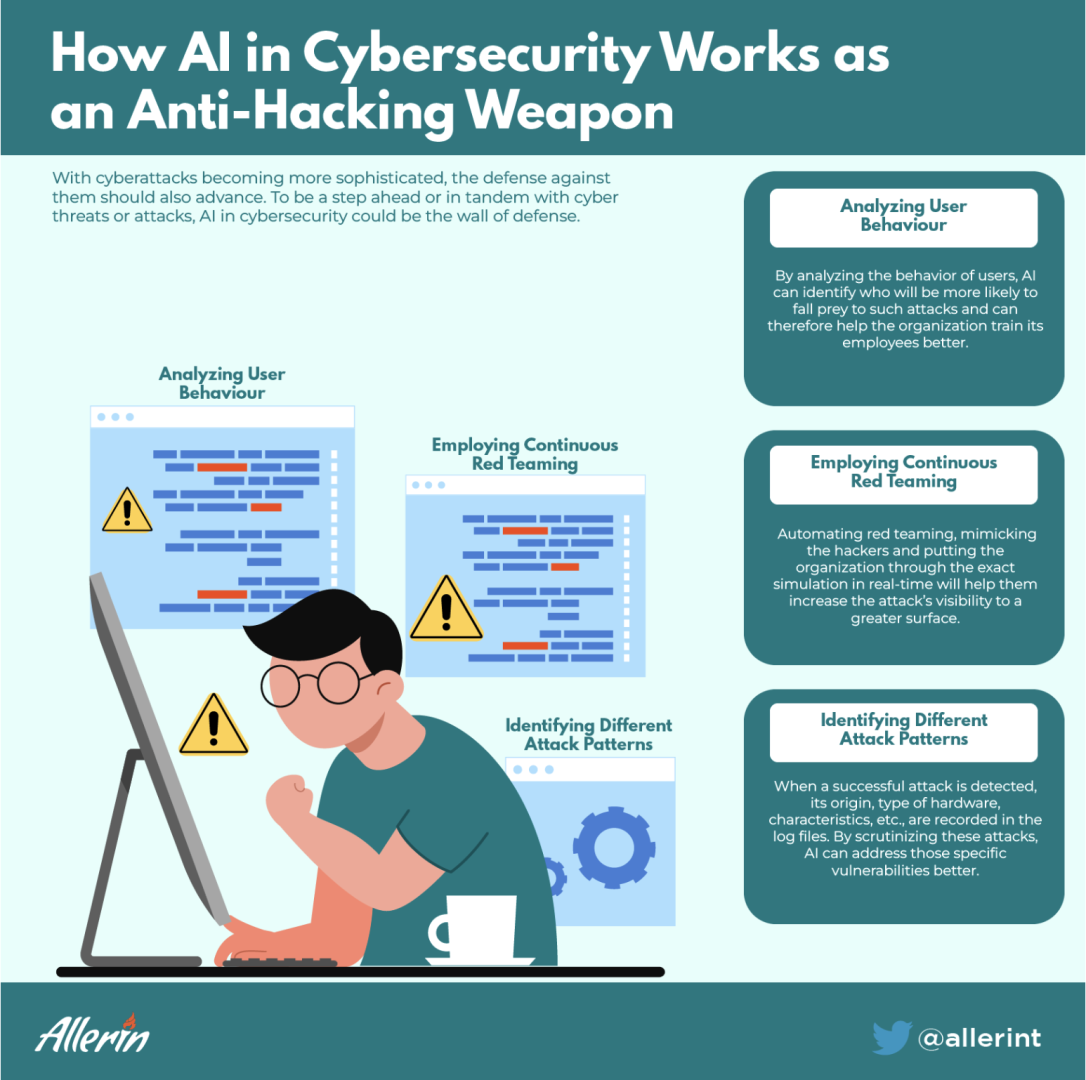
To test the awareness and vigilance of employees, AI will send phishing emails and understand their behavior. Cybercriminals use email phishing as a method to get direct access to an organization's system. It requires just one weak link to create a domino effect for the entire security system to crumble. By analyzing the behavior of users, AI can identify who will be more likely to fall prey to such attacks and can therefore help the organization train its employees better.
To thoroughly test the cyber resilience, incident response and threat detection capabilities, red teaming must be employed. It is intelligent security that assesses the cybersecurity strength of an organization by replicating the exact tactics, processes, and techniques used by hackers to weaken or damage the security system. Automating red teaming, mimicking the hackers and putting the organization through the exact simulation in real-time will help them increase the attack's visibility to a greater surface. This will enable the organization to understand the vulnerabilities in its network of systems and take the required actions.
A logging mechanism is included in all tools for computer network management. These log files are privy to ample information sources that note and project user behavior, attempts to access the network, application issues, and more. When a successful attack is detected, its origin, type of hardware, characteristics, etc., are recorded in the log files. By scrutinizing these attacks, AI can address those specific vulnerabilities better.
It is not a hidden fact that cybercriminals are getting more powerful in infiltrating an organization's network systems. To give a proper fight, AI in cybersecurity has become one of the most required solutions. It will allow organizations to enhance their cybersecurity performance by finding any vulnerabilities and patching them up.
Naveen is the Founder and CEO of Allerin, a software solutions provider that delivers innovative and agile solutions that enable to automate, inspire and impress. He is a seasoned professional with more than 20 years of experience, with extensive experience in customizing open source products for cost optimizations of large scale IT deployment. He is currently working on Internet of Things solutions with Big Data Analytics. Naveen completed his programming qualifications in various Indian institutes.
Leave your comments
Post comment as a guest