Comments
- No comments found

In one of my recent CXO Spice Talk shows, a guest and I were talking about a foreseeable future where an individual – like us – would have a petaflop of computing power and a petabyte of storage.
What can we do with that? Well, instead of Zoom, we might send our 3D hologram to the customer meeting or beam up a performance dashboard as easily as Tony Stark, my favorite Avenger character.
This is the future: more data, bigger files, greater computing power. Not only that, but the future is approaching fast.
Technology transformation is, of course, rapidly underway in the workplace too. We are seeing the deployment of Artificial Intelligence, the acceleration of edge computing where devices themselves shoulder processing responsibilities, and a tsunami of connected IoT devices predicted to reach 500 billion by 2030, per a report by Gartner.
Today, though, I would like to explore a topic that is much larger than work. It is the dignity of an individual. The topic is creativity.
Creativity is very important to me. I believe every individual is creative. On the surface, we talk about writers and filmmakers and we call them creatives. However, a person who solves a critical problem, makes a life goal happen, starts a business or even just bakes a beautiful cake is creative.
According to a report from LinkedIn, creativity is the most in-demand soft skill and is second overall to cloud computing, which is a hard skill.
So with a rise in technology, which I believe must positively impact people to be worthwhile, how will our creativity remain secure?
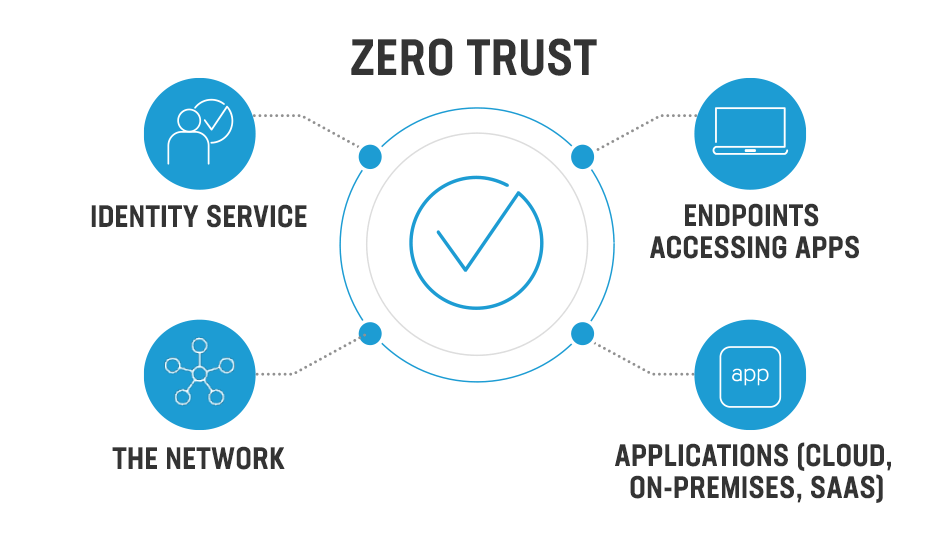
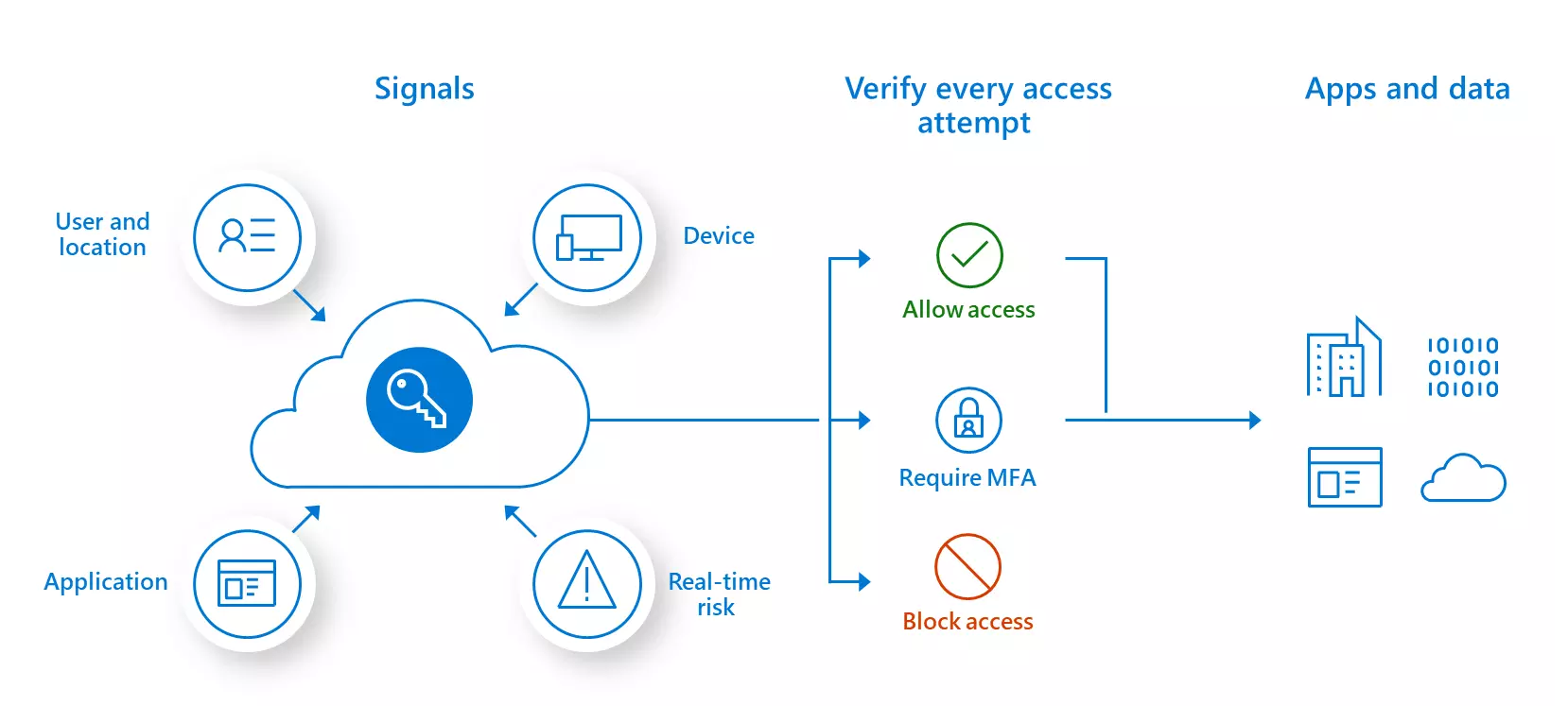
The premise of zero trust security is assuming your operation has been breached. There’s a reason why this is important at this point in time. In an article written by Accenture’s security expert Gabe Albert “corporate network boundaries are disappearing” which inspires a contextual-based approach to security.
I like how IBM describes zero trust: “Security wrapped around every user, every device, every connection – every time.” This simple yet profound view mimics the creative process.
Last year, I published my book Ascend Your Start-up: Conquer the 5 Disconnects to Accelerate Growth. The creative process was as disciplined as it was fluid. There are many micro-interactions that lead to a book. I don’t think most people sit down to write a large composition. Instead, the creative process is a string of many micro-interactions with your subject matter. While I set word count goals, I also left plenty of space to imagine the book, explore what-if scenarios, and write stories about my climb up Mt. Everest to underscore the 5 disconnects.
The digital aspect of creativity was ever present in my efforts: collaborating with my publisher, saving different versions in the cloud, conducting research and interviews, drafting thoughts on my phone. Upon publication, we even transformed part of the book into an NFT.
I remember once, while working on a PowerPoint for a global event, someone had dropped in a picture I did not recognize and changed some of the content. I found out who it was and how they did it and applied a patch to my computer to prevent it from happening again. What would have happened if my book had been compromised, if whole pages had been changed or deleted?
As we create and innovate, how do we secure the world we create in?
For enterprise companies, this is one reason why cybersecurity looks different than in the past. We are no longer playing defense. Cybersecurity goes far beyond phishing and virus protection or cyber-training new employees during the onboarding process.
Global cybercrime now tops almost $600 billion, according to online protection company McAfee. It’s time to change up the cybersecurity playbook.
Creativity is the fuel by which enterprise companies will succeed. We are becoming “enterprise creatives,” a term I use to describe people as we shift from process-driven jobs to more critical thinking roles.
IBM has developed solutions for enterprise creatives like Guardium Solution which keeps data where it resides rather than moving it to another place. It’s like keeping the data where the creative magic happens! Guardium also helps you break down silos for better risk assessment across data, identity and security operations center teams. Collaboration is a huge component of creativity for enterprise creatives.
Comparing, again, the enterprise world with the creative process we see the timing of a security matter. While working on my book, there were huge edits I made after the first draft. However, had I waited until the book’s near completion, those changes would have been almost irrevocable. IBM’s Security QRadar Security Information and Event Management (SIEM) helps security teams detect threats earlier so it’s easier to respond and fix the problem.
IBM’s solutions are an integral part of a zero trust strategy, accelerating a threat’s analysis and remediation – so you can use and connect tools of choice to your zero trust strategy with ease.
Playing defense holds us back from creating and innovating. According to the IBM Cyber Security Intelligence Index Report, 95% of all cyber-attacks result from human error, building security that goes where we create gives us the freedom to explore and create without worry or compromise – whether we are writing a book or merely beaming up our hologram to bring world-changing ideas to the stage.
What is your creative muse today?
From time to time, IBM collaborates with industry thought leaders to share their opinions and insights on current technology trends. The opinions in this article are my own, and do not necessarily reflect the views of BBN Times and IBM.
Helen Yu is a Global Top 20 thought leader in 10 categories, including digital transformation, artificial intelligence, cloud computing, cybersecurity, internet of things and marketing. She is a Board Director, Fortune 500 Advisor, WSJ Best Selling & Award Winning Author, Keynote Speaker, Top 50 Women in Tech and IBM Top 10 Global Thought Leader in Digital Transformation. She is also the Founder & CEO of Tigon Advisory, a CXO-as-a-Service growth accelerator, which multiplies growth opportunities from startups to large enterprises. Helen collaborated with prestigious organizations including Intel, VMware, Salesforce, Cisco, Qualcomm, AT&T, IBM, Microsoft and Vodafone. She is also the author of Ascend Your Start-Up.
Leave your comments
Post comment as a guest