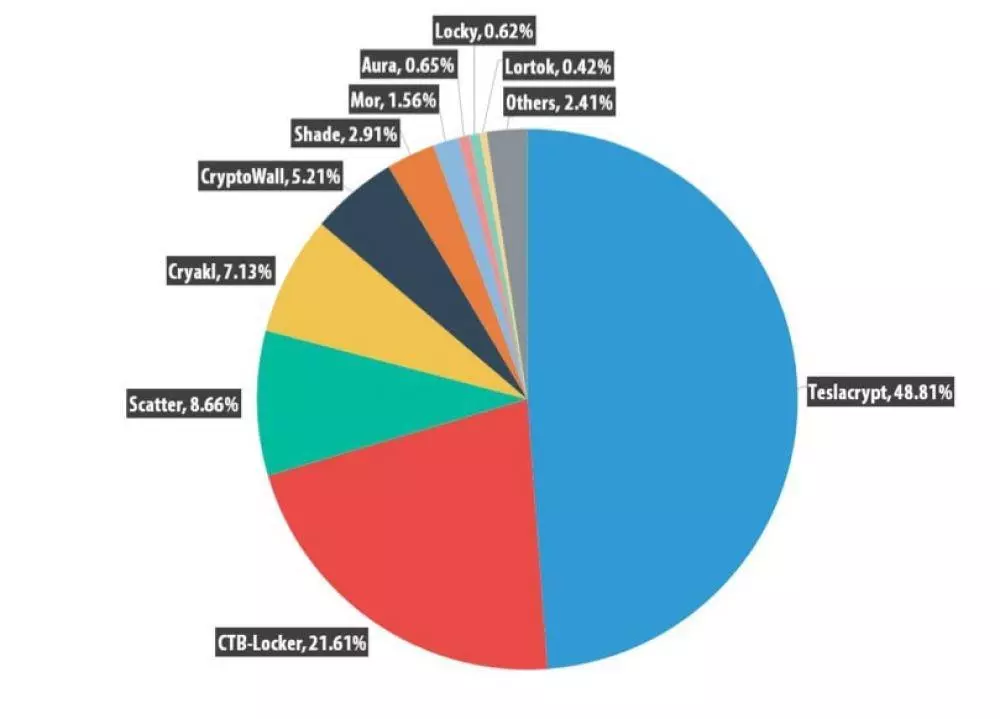
As cybercriminals get more intelligent, we must be more vigilant and conscientious than before in taking preventive measures. Basic security measures include the use of firewalls, anti-virus software, intrusion detection and prevention systems, unique encryption and login passwords, and casting cyber insurance policy as a safety net.
Another area we must consider is the cybersecurity regulation. In a nutshell, cybersecurity regulation is an act that gives an added push for companies to seek professional assistance in protecting their systems and information from cybercriminals. It is, therefore, imperative that we include cybersecurity in our regulatory examinations to make sure that our systems are safeguarded always.
On a national level, Singapore takes cybersecurity threats very seriously. As Singapore has the highest level of digital connectivity in the world, a cyberattack on our critical information infrastructures or CIIs will have a colossal impact countrywide.
Singapore’s current Computer Misuse and Cybersecurity Act focuses on cybercrime per se. However, CSA Chief Executive David Koh emphasized that we need a “more multi-faceted bill to oversee the evolving cybersecurity landscape.” That called for the Ministry of Communications and Information (MCI) and the Cyber Security Agency of Singapore (CSA) to seek feedback on the proposed Cybersecurity Bill in 2016.
In the same year, our Prime Minister Lee Hsien Loong rolled out Singapore’s Cybersecurity Strategy to create a more resilient and trusted environment for our nation.
Four pillars underpin its strategy:
1. Educate the public about internet security and online safety
2. Step up the protection of Singapore's essential services in key sectors such as emergency
services, e-Government, banking and finance, utilities, transport and healthcare
3. Establish a professional workforce for the cybersecurity sector and this includes creating opportunities for existing professionals (e.g. the Cyber Security Associates and Technologists (CSAT) program allows existing ICT professionals with three years of work experience to
switch over to cybersecurity roles via a six-month training scheme)
4. Build stronger international relationships with regard to cyber incident response and even
prosecuting cybercrime that crosses national boundaries
In July of 2017, the MCI and the CSA released a new Singapore Cybersecurity Bill for public consultation. The draft bill aims to be a broader omnibus cybersecurity law, highlighting a coordinated national approach to cybersecurity with provisions applying equally to both public and private sectors.
The following are the key proposals under the draft Cybersecurity Bill:
1. Appointment of Commissioner of Cybersecurity:
The Bill will vest in the CSA's chief as Commissioner of Cybersecurity to investigate threats and incidents to ensure that essential services in key sectors - such as emergency services, e-Government, banking and finance, utilities, transport and healthcare - are not disrupted in the event of a cyberattack.
2. Critical Information Infrastructure
: The Bill aims to protect critical information infrastructure (CII) across both public and private sectors, requiring all organisations to share information to support cybercrime headed by the CSA. Banking and privacy rules that forbid the sharing of confidential information will be superseded by the Cybersecurity Bill.
3. Measures to be Undertaken by CII Owners in Response to Cybersecurity Threats and Incidents
: CII owners are required to:
a. Notify the Commissioner of the CII suffering a cybersecurity attack;
b. Conduct regular system audits by a Commissioner-approved third-party;
c. Conduct regular risk assessments of the CII;
d. Comply with directions issued by the Commissioner, including providing access to premises, computers or information during investigations.
4. CII Designation
The Commissioner may identify and designate new systems as CII during times of national emergency. The designation of a computer or computer system as a CII is an official secret under the Official Secrets Act.
5. Regulation of Cybersecurity Service Providers
Cybersecurity providers performing either investigative work (e.g. hacking and forensic examination) or non-investigative work (e.g. managed security operations) must meet basic requirements to qualify for a license. Investigative cybersecurity service practitioners such as hackers must also apply for individual licenses. Unlicensed providers will face a maximum fine of S$50,000, imprisonment of up to two years, or both.
CSA also reported that Singapore will collaborate with Germany to boost both countries’ cybersecurity.
The draft Cybersecurity Bill will undergo the legislative process and is expected to be passed into law in 2018. It would be interesting to see if there would be changes in the draft after the public consultation held in August 2017.
As we grow to be more reliant on information technology, with e-commerce becoming an important contributing sector to our economy, we must take cybersecurity very seriously before it’s too late. Cybersecurity is vital to our business operations, especially in safety-critical systems, such as emergency response, and to the protection of our infrastructure systems.
So, what have we done to combat cybercriminals, and in building a resilient and robust security system alongside our government’s anti-cyberattack initiatives? And how have we responded to Singapore’s cybersecurity regulation? The clock has started ticking.
For other articles on Cybersecurity, IT, and Sales Leadership, I invite you to my blog at blog.nagrosst.com



Leave your comments
Post comment as a guest