Comments
- No comments found

The Internet of Things (IoT) has revolutionized the way we interact with technology, from our homes to our workplaces.
IoT devices are used to monitor, control, and optimize everything from energy usage to inventory management. While IoT technology offers many benefits, it also comes with risks. In particular, turnkey IoT solutions, which provide complete systems that are ready to be deployed, pose unique challenges and potential risks. In this article, we will explore the risks associated with turnkey IoT solutions and how to mitigate them.
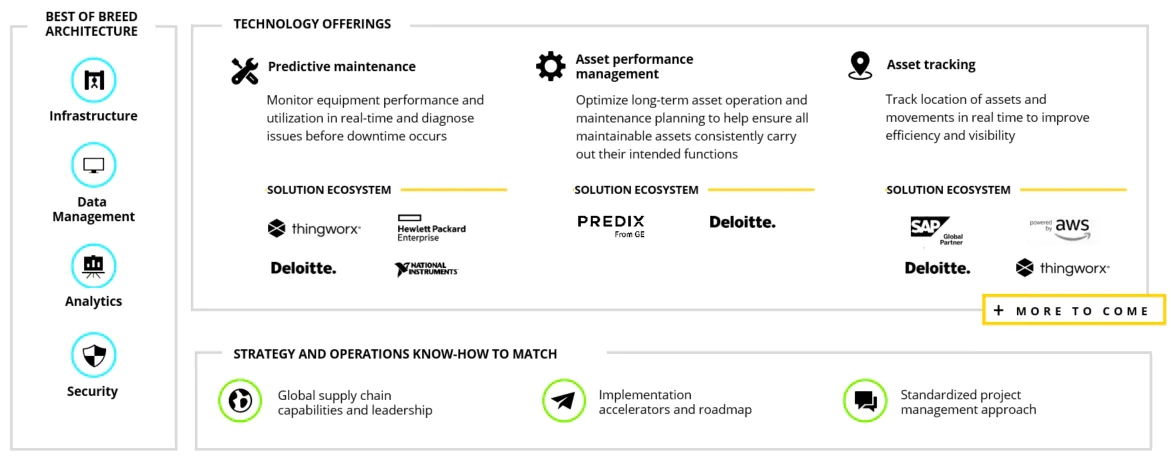
Turnkey IoT solutions are complete systems that are ready to be deployed. They typically include hardware, software, and connectivity, as well as services such as data analytics and maintenance. Turnkey IoT solutions are designed to be easy to use and deploy, making them popular with organizations that lack the resources or expertise to build their own IoT systems from scratch.
To enhance IoT security measures in the production process, it's crucial to seek info on counterfeit mitigation strategies to safeguard products.
While turnkey IoT solutions offer many benefits, they also come with risks. These risks can be classified into three main categories: security risks, privacy risks, and legal and compliance risks.
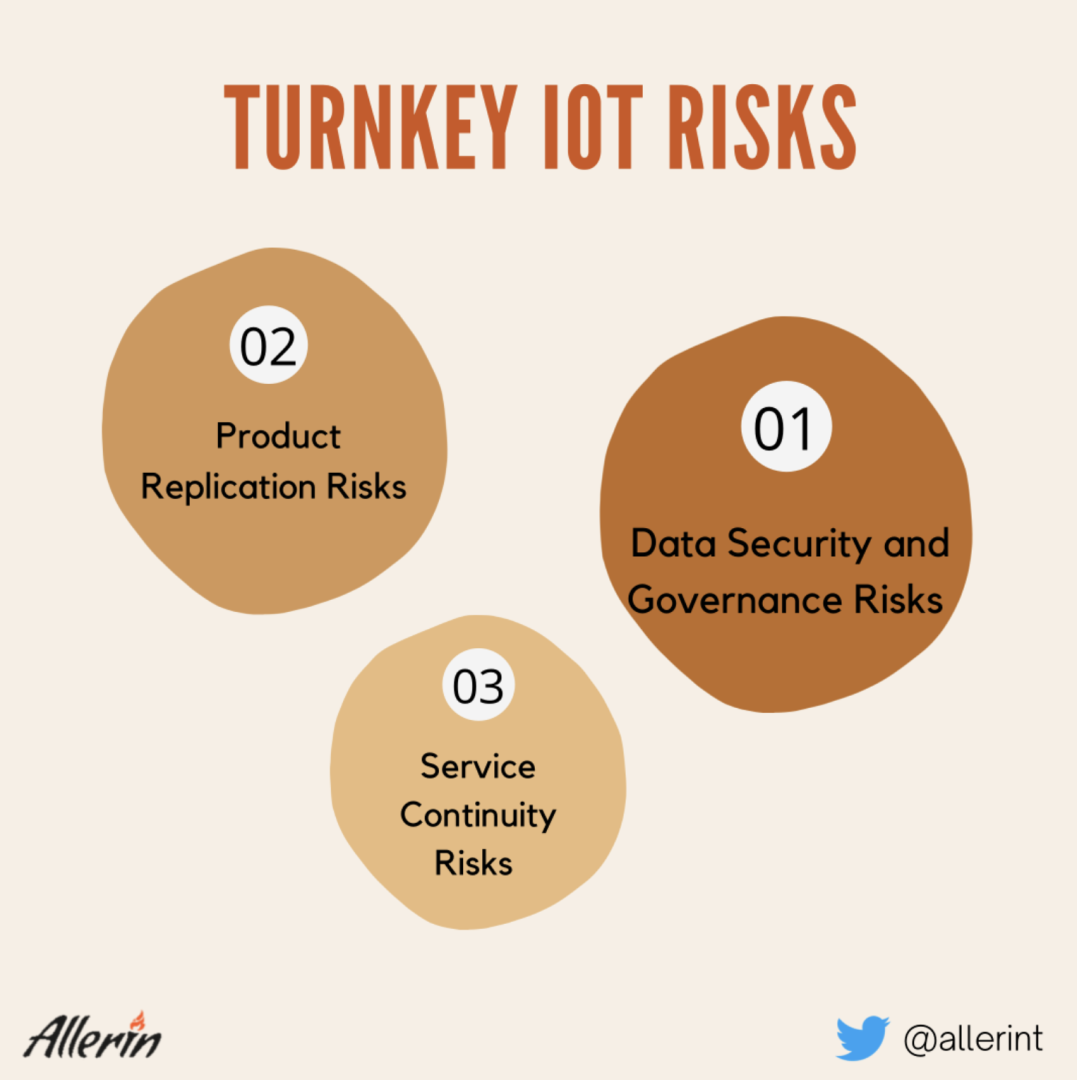
Privacy is a major concern when it comes to turnkey IoT solutions. IoT devices can collect large amounts of data about users, including personal information such as names, addresses, and even biometric data. This data can be used for nefarious purposes, such as identity theft, or sold to third parties without the user's consent.
One of the biggest risks associated with turnkey IoT solutions is security. IoT devices are vulnerable to cyber attacks, and turnkey solutions are no exception. Hackers can use IoT devices as a gateway into a company's network, stealing sensitive data, disrupting operations, and even causing physical damage. In some cases, hackers have used compromised IoT devices to launch large-scale attacks on other targets.
Turnkey IoT solutions also pose legal and compliance risks. Companies that collect personal data are subject to a variety of regulations, including the EU's General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA). Companies that fail to comply with these regulations can face significant fines and damage to their reputation.
IoT devices are often connected to the internet, making them vulnerable to cyber attacks. The large amounts of data that are generated by these devices are attractive to cybercriminals, who may seek to steal sensitive data or use it to carry out malicious activities.
One of the main concerns with IoT devices is that they are often designed with security as an afterthought. This means that many devices may have vulnerabilities that could be exploited by attackers. Furthermore, the sheer number of devices that are being used in IoT networks means that managing and securing them all can be a significant challenge.
There have been several high-profile examples of data breaches involving IoT devices. For example, in 2016, hackers used a network of compromised IoT devices to carry out a massive distributed denial of service (DDoS) attack on a domain name system (DNS) provider. This attack caused significant disruption to many popular websites and services.
One of the key benefits of IoT technology is that it enables different devices and systems to communicate and work together. However, achieving this kind of interoperability can be challenging, particularly when devices are developed by different manufacturers.
When devices are unable to communicate with each other, it can create inefficiencies and limit the usefulness of IoT networks. For example, a smart home system may be unable to integrate with a smart car system, preventing the user from accessing certain features or automating certain tasks.
Interoperability can also create security risks, particularly if different devices have different security protocols or vulnerabilities. Attackers may be able to exploit these differences to gain unauthorized access to devices or networks.
IoT devices are subject to a wide range of regulatory and compliance requirements, particularly in industries such as healthcare and finance. For example, the Health Insurance Portability and Accountability Act (HIPAA) in the United States sets standards for the storage and transmission of healthcare data.
Organizations that fail to comply with these regulations may face significant fines and other penalties. Ensuring compliance with these regulations can be challenging, particularly as new devices and technologies are introduced.
The rise of turnkey IoT solutions has brought numerous benefits to companies looking to enhance their operations and gain a competitive edge. However, with these benefits come potential risks, such as security vulnerabilities, data breaches, and privacy concerns. Fortunately, companies can take steps to mitigate these risks and ensure the safe deployment of turnkey IoT solutions.
Firstly, conducting a risk assessment is a critical step in identifying potential vulnerabilities and threats. A thorough risk assessment can help companies understand the specific risks associated with their turnkey IoT solution and develop strategies to address them.
Secondly, selecting a reputable provider is essential. Companies should choose a provider with a proven track record of security and privacy. Checking references and conducting due diligence can help in selecting the most suitable provider.
Thirdly, implementing strong security measures is crucial. Companies should implement security measures such as two-factor authentication, encryption, and access controls to protect their IoT devices and data. These security measures should be continuously monitored and updated to stay ahead of potential vulnerabilities.
Lastly, regularly monitoring and updating IoT devices is essential. Companies should ensure their devices are secure and up-to-date with the latest software patches to address any identified vulnerabilities.
The benefits of turnkey IoT solutions are numerous, but companies must be vigilant to mitigate the potential risks associated with them. By following the best practices outlined above, companies can deploy turnkey IoT solutions confidently and securely.

Selecting a turnkey IoT provider is a crucial decision for companies that want to implement IoT solutions. It is essential to choose a provider that can ensure the security and privacy of your IoT devices and data. Here are some best practices to consider when selecting a turnkey IoT provider:
It is crucial to choose a provider with a proven track record of security and privacy. Look for providers that have experience working with similar clients in your industry and ask for references. Conduct research on the provider's reputation by checking online reviews and industry publications.
IoT technology is continuously evolving, and regular updates and maintenance are essential to ensure optimal performance and security of IoT devices. Choose a provider that offers regular updates and maintenance to ensure your devices are always up-to-date.
The security of your IoT devices and data is critical. It is essential to choose a provider that offers strong encryption and access controls. Encryption ensures that your data is protected, while access controls restrict access to your devices and data to only authorized personnel.
When selecting a turnkey IoT provider, it is crucial to consider their data privacy and compliance policies. Ensure that the provider follows data privacy laws and regulations such as the General Data Protection Regulation (GDPR) and the California Consumer Privacy Act (CCPA). Additionally, ask the provider about their security and privacy practices, including their data retention policies and data breach response plan.
Choosing a turnkey IoT provider is a critical step towards implementing IoT solutions. Companies must choose a provider that can ensure the security and privacy of their devices and data. By following the best practices outlined above, companies can make an informed decision when selecting a turnkey IoT provider.
IoT technology has the potential to revolutionize a wide range of industries, from healthcare and manufacturing to agriculture and transportation. However, as with any new technology, there are also significant risks and challenges associated with IoT.
Organizations that are considering implementing IoT technology must carefully consider these risks and develop strategies for mitigating them. This may involve investing in security and data protection measures, developing clear policies and procedures for IoT use, and staying up to date with regulatory and compliance requirements.
By taking a proactive approach to IoT risk management, organizations can harness the power of this technology while minimizing its potential downsides.
Naveen is the Founder and CEO of Allerin, a software solutions provider that delivers innovative and agile solutions that enable to automate, inspire and impress. He is a seasoned professional with more than 20 years of experience, with extensive experience in customizing open source products for cost optimizations of large scale IT deployment. He is currently working on Internet of Things solutions with Big Data Analytics. Naveen completed his programming qualifications in various Indian institutes.
Leave your comments
Post comment as a guest