Comments
- No comments found

Imagine for a moment your social security and driver's license numbers are stolen – and not by your own devices.
You didn’t leave your purse in an unlocked car nor drop your wallet at the store. No, this thievery happened under someone else’s watch. Add to that, the breach happened within a company you once worked for or currently patronize. You are not alone in feeling violated; more than five million people are affected, although that doesn’t provide any sense of comfort.
Like many unexpected crises, your other worries now seem small. With your personal information at risk, you wonder: How do I keep my information safe as digital transformation unfolds and cloud computing becomes the norm?
The scenario outlined above is a true story. The personal data of customers and former employees of Infinity Insurance were breached in December of 2020. The story underscores the growing importance of data privacy impact. It’s a different kind of security issue. There is no easy fix when personal data is stolen. You can’t call someone and get a new driver’s license or social security number like you can with a credit card. It’s much more complicated.
Stories of data misuse take many different forms. What if your sensitive information got out because a company you worked for or purchased from sold its data? Or because an employee at that organization copied your info over to another location to use a different analysis application? How much worse would you feel then? There is a growing concern around how much of our private personal data is being sold or used under our noses, who has access to what information, and how information from multiple sources can be used in conjunction to identify the original individual.
The impact is, however, much bigger than we think. In its coverage on the topic, CRN magazine cited “more than 98.2 million individuals were impacted by the 10 biggest data breaches in the first half of 2021, with three of the 10 largest breaches occurring at technology companies.” This insight, collected by the ITRC and the U.S. Department of Health and Human Services, demonstrates the precarious intersection of digital transformation and data privacy. On the flip side, the penalty for breach of data privacy is hefty. Amazon’s fine of $886 million from the Luxembourg’s National Commission for Data Privacy Is unprecedented. I see numbers like these rising in the future for companies unprepared or unconcerned about data privacy.
Freedom is a topic I often talk about. What I mean here is cultivating freedom during a time when we are experiencing a data explosion and evolution of technology, one where opportunities from data and the risks are both enormous.
We see this delicate balance between freedom and protecting data privacy all around us. For example, in the field of healthcare, how do you anonymize sensitive information about patients while enabling data to be used to optimize patient care? Or in the banking industry, how do you protect personal information while creating a seamless customer experience?
Worrying about security or privacy of information erodes our personal freedom by creating anxiety and distrust. So we must ask ourselves: How do we turn knowledge into wisdom? Data into insights? Our values into trust?
There are four areas to consider:
“Build” It: Establish data governance goals and objectives by making it part of the business strategy. Define and implement a data stewardship program to align with business outcomes, streamline and standardize data to ensure quality and improve efficiency, establish master data management, and track on-going improvement. Understand who is consuming what data, who will have the access to what data and why the data is important.
“Share” It: Upskill and educate your workforce to meet the demands of data privacy across the organization. Make everyone a “data expert” so that employees understand their responsibilities and the role they play to ensure privacy standards are upheld. This includes learning lessons when failures occur. Infinity Insurance vowed to look at the results of its security investigation and strengthen its network security and cybersecurity program.
“Own” It: It’s not about data senders, it’s about impact. What will you drive and how do you maximize outcomes? Accountability is critical. With all these different data available, the key is to gain actionable insights for more effective business decisions – and hold leaders accountable. They must “own” it. Imagine what your customers, peers, employees and supply chain partners would think if they are 100% confident you would be willing to defend data privacy. It takes the idea of explainability to the next level and forces people to consider how they would justify the usage of personal information.
“Set” It: Make policy a priority by setting down a precedent for monitoring data privacy. More companies are prioritizing data privacy at the board level with dedicated committees created to help solve this problem.
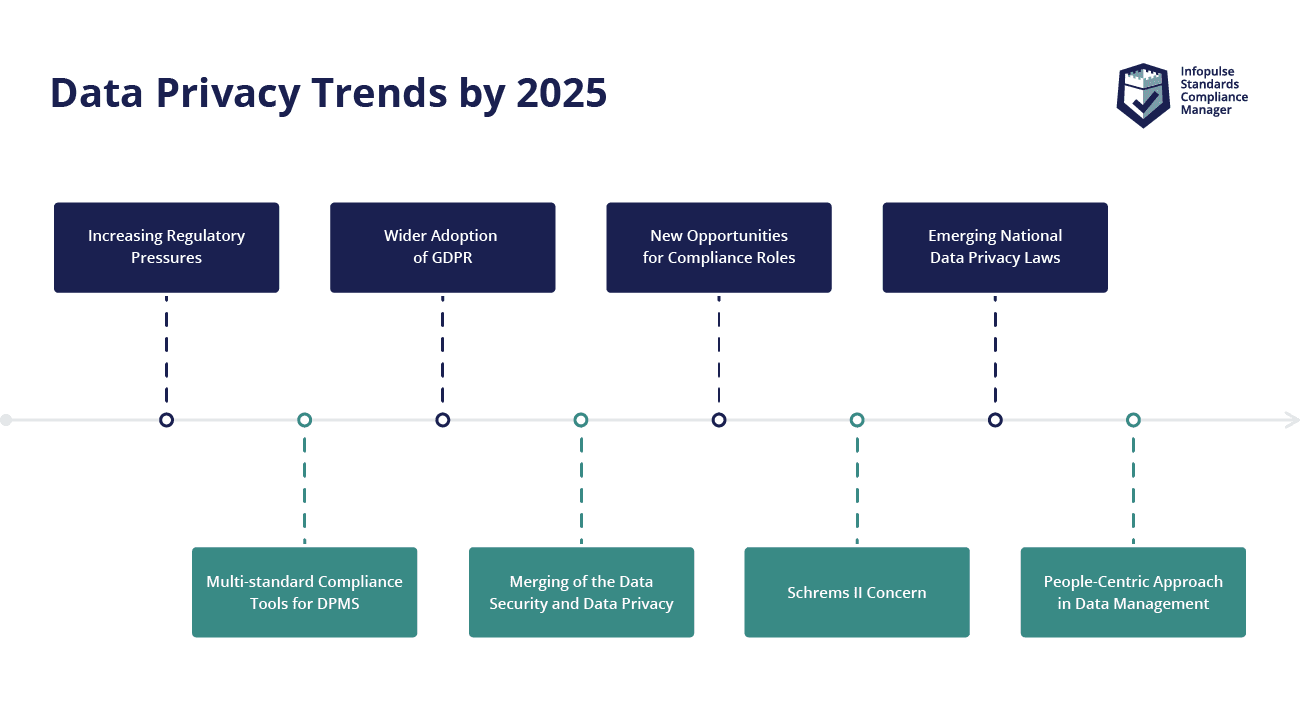
In Gartner’s “Predicts 2021: Data and Analytics Strategies to Govern, Scale and Transform Digital Business,” two compelling predictions further support the perfect storm created when digital transformation, data privacy and cloud collide
A look ahead tells us that there will be more threats, more AI-driven data, more people impacted (especially with the growing number of devices worldwide) and more vulnerable entryways as we enter a multi-cloud world.
There are several tech innovators who are developing solutions at the intersection of digital transformation (cloud) and data. IBM is one of them.
IBM Cloud Pak® for Data allows organizations to deploy a unified privacy framework designed to help companies fully understand and manage how sensitive data is used throughout their organizations. Key attributes include data governance, data privacy, risk management and data security within a collaborative platform, providing users a universal view of PII across their businesses. It answers the who-what-where-when questions behind data access.
One critical point of difference for IBM Cloud Pak for Data is that data remains stationary, meaning data can be used without moving it from its source for AI and analytics initiatives. Advanced capabilities such as automated masking of highly sensitive data and de-identification of data support data privacy. Automating data protection – especially for high-risk data – lessens the possibility of human error or misuse.

Hopefully, walking in the shoes of those impacted by the Infinity Insurance security breach showed you how data privacy becomes top of mind for people when a crisis occurs. Future-forward leaders, however, will prepare. They will lead with accountability, realizing that protecting people as well as staying ahead of growing regulations and public perception on data usage leads to stronger data privacy with accountability.
James M. Strock, author of Serve to Lead, writes: "In the wired world of the 21st century, advancing shared values creates value.” It is not often values and technology are written in the same sentence – but they should be. I can’t think of a better viewpoint than values to guide our companies while making IT decisions, setting down IT policies and supporting the business strategy.
Disclaimer: From time to time, IBM invites industry thought leaders to share their opinions and insights on current technology trends. The opinions in this article are my own, and do not necessarily reflect the views of IBM & BBN Times.
Helen Yu is a Global Top 20 thought leader in 10 categories, including digital transformation, artificial intelligence, cloud computing, cybersecurity, internet of things and marketing. She is a Board Director, Fortune 500 Advisor, WSJ Best Selling & Award Winning Author, Keynote Speaker, Top 50 Women in Tech and IBM Top 10 Global Thought Leader in Digital Transformation. She is also the Founder & CEO of Tigon Advisory, a CXO-as-a-Service growth accelerator, which multiplies growth opportunities from startups to large enterprises. Helen collaborated with prestigious organizations including Intel, VMware, Salesforce, Cisco, Qualcomm, AT&T, IBM, Microsoft and Vodafone. She is also the author of Ascend Your Start-Up.
Leave your comments
Post comment as a guest