Comments
- No comments found

Blockchain has popularly grown into a promising mitigation technology for cybersecurity.
Cybersecurity is important because all our data is stored on the web.
A hack could put our credentials on the line. How blockchain can help in improving cybersecurity is interesting to see.
The credentials that we use to gain access to our bank accounts, investments, medical records and other sensitive data are typically stored in databases owned by banks, financial institutions, hospitals and other organizations respectively. The storage architecture these organizations employ present a single point of attack for potential malicious intent. The strength and features of the blockchain technology is going to improve the way cybersecurity is implemented.
Blockchain technology is a distributed ledger, which eliminates the need for a third party organization, and makes use of a distributed database. This helps in lowering the transaction costs. Besides, third party organizations use a centralized database, which enhances the risk of fraudulent activity.
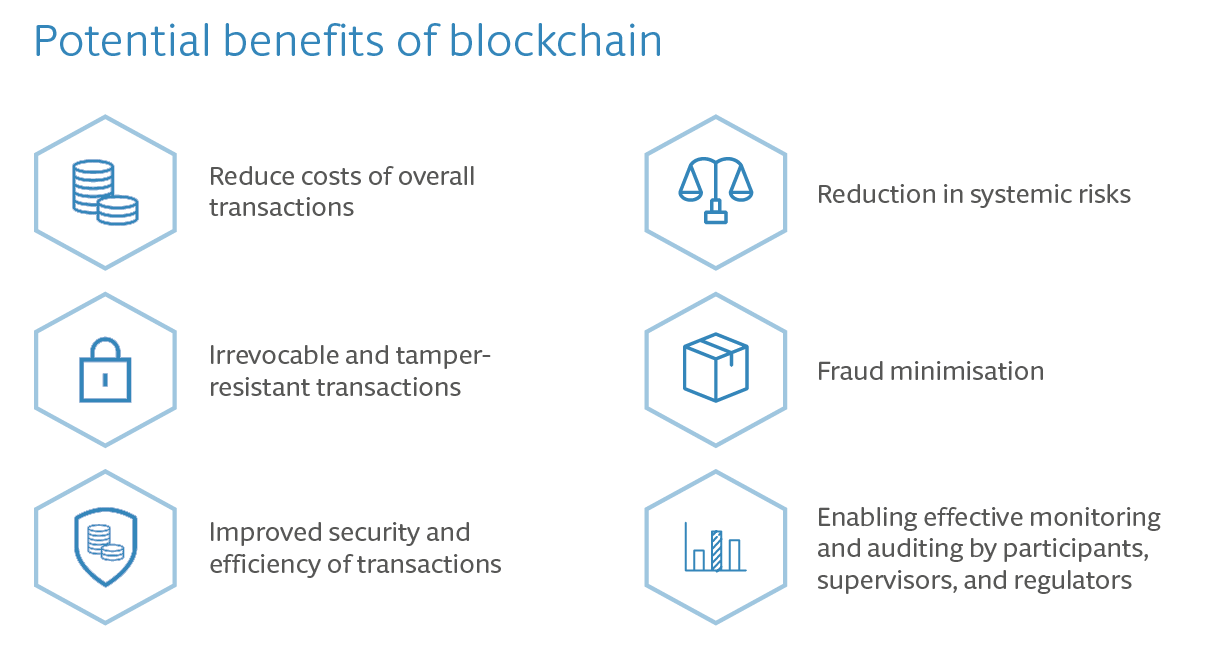
Since a blockchain system is protected with the help of ledgers and cryptographic keys, attacking and manipulating it becomes extremely difficult. Blockchain decentralizes the systems by distributing ledger data on several systems rather than storing them on one single network. This allows the technology to focus on gathering data rather than worrying about any data being stolen. Thus, decentralization has led to an improved efficiency in blockchain-operated systems.
For a blockchain system to be penetrated, the attacker must intrude into every system on the network to manipulate the data that is stored on the network. The number of systems stored on every network can be in millions. Since domain editing rights are only given to those who require them, the hacker won’t get the right to edit and manipulate the data even after hacking a million of systems.
Since such manipulation of data on the network has never taken place on the blockchain, it is not an easy task for any attacker.
While we store our data on a blockchain system, the threat of a possible hack gets eliminated. Everytime our data is stored or inserted into blockchain ledgers, a new block is created. This block further stores a key that is cryptographically created. This key becomes the unlocking key for the next record that is to be stored onto the ledger. In this manner, the data is extremely secure.
Furthermore, as already mentioned above, the data is stored in a decentralized form.
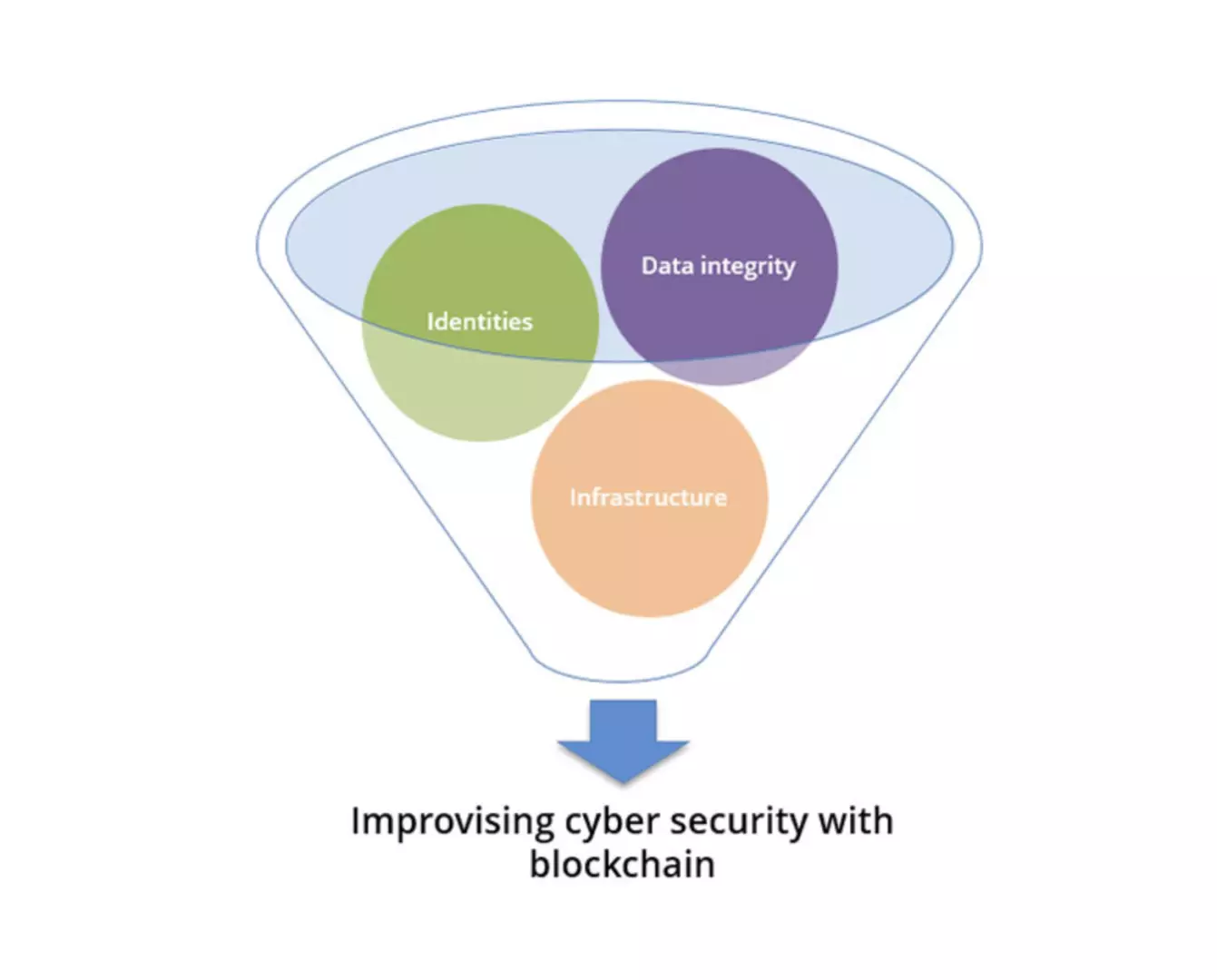
The hashing feature of blockchain technology is one of its underlying qualities that makes it such a prominent technology. Using cryptography and the hashing algorithm, blockchain technology converts the data stored in our ledgers. This hash encrypts the data and stores it in such a language that the data can only be decrypted using keys stored in the systems.
Other than cybersecurity, blockchain has many applications in several fields that help in maintaining and securing data. The fields where this technology is already showing its ability are finance, supply chain management, and blockchain-enabled smart contracts.
It is becoming increasingly interesting to see where blockchain steps foot next.
While the old threats linger, new and unexpected cybersecurity threats will continue to emerge. Blockchain will prove to be a powerful tool for experts and engineers to harden their systems against a plethora of threats that surround us. And this is especially true as far as centralized weaknesses and single points of failure are the concern.
Naveen is the Founder and CEO of Allerin, a software solutions provider that delivers innovative and agile solutions that enable to automate, inspire and impress. He is a seasoned professional with more than 20 years of experience, with extensive experience in customizing open source products for cost optimizations of large scale IT deployment. He is currently working on Internet of Things solutions with Big Data Analytics. Naveen completed his programming qualifications in various Indian institutes.
Leave your comments
Post comment as a guest