Comments
- No comments found

Smart manufacturing has the potential to improve the manufacturing industry as a whole.
The Internet of Things (IoT) combined with broadband connectivity have enabled us to create smart factories, where every aspect of the manufacturing process can be monitored and optimized using artificial intelligence and predictive analytics. However, as the number of connected devices increase, so do potential security risks, making network security a critical consideration in the design and implementation of smart factories. In this newsletter, we’ll be discussing the advantages of smart manufacturing, the role of 5G in enabling it, and the importance of network security for protecting digital assets and preventing cyber threats.
I was thrilled to have hosted AT&T Business #BizTalks with industry thought leader Dez Blanchfield as my guest. We explored the exciting world of smart manufacturing, benefits of IoT, 5G, MEC in making informed decisions, forecast demand and prevent downtime while prioritizing robust network security.
Here is a recap of our discussion:
My POV (@YuHelenYu): Smart factories mean applying smart technology to the business of manufacturing. Through connectivity solutions like IoT, Video Intelligence and 5G, you can use predictive analytics to make informed decisions, forecast demand, and prevent downtime. My ideal factory would also have an effective cybersecurity strategy that extends beyond the factory to remote workers, third-party vendors, and suppliers to help protect vulnerabilities that hackers may target.
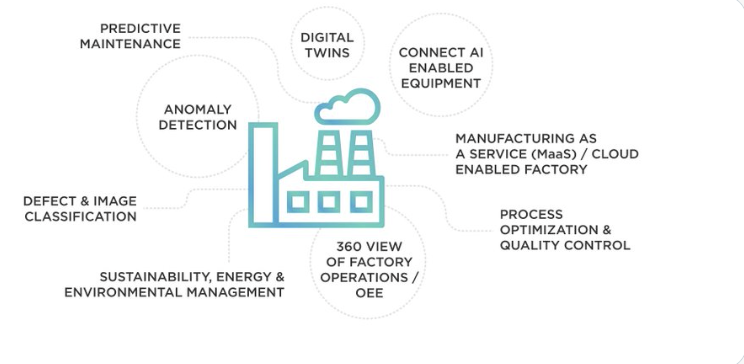
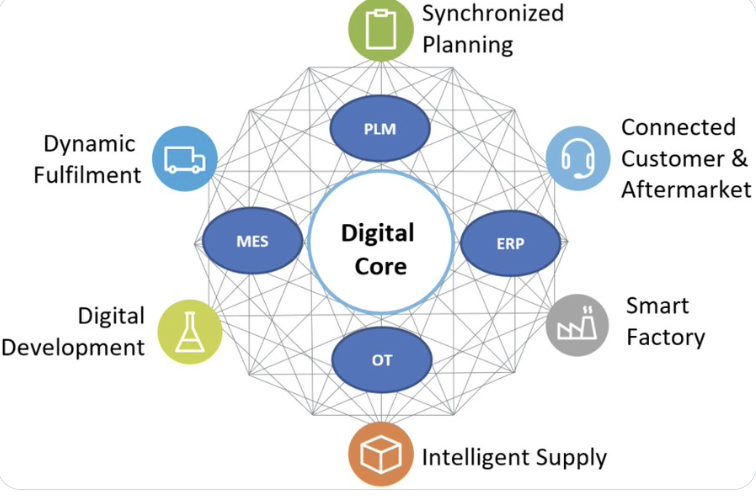
Dez Blanchfield (@Dez_Blanchfield) uses an infographic to illustrate key components of smart factory. “The key driver to smart manufacturing is digital technologies and fast telecommunications, both are enablers of innovation and digital.”
Maryson W. (@Connoisseur_RPA) added: “Smart factories maximize on edge computing with more than fortified cybersecurity. Industry 4.0 would require more of frameworks, than mere checklists, strategies, or plans. As digital transformation culminates into a race for digital survival, the toughest will see Industry 5.0.
My POV: 5G is the catalyst because it offers higher bandwidth and lower latency and enable real-time communication between machines, sensors, cameras, and human. It allows for more machines to be connected to the network and to communicate with each other and optimize production processes in real-time. 5G enables manufactures use sensors to track location and condition of inventory as they move through the supply chain and help prevent delays and reduce waste. It enables the use of Augmented Reality in manufacturing. Technicians can use AR to visualize and troubleshoot problems.
Dez Blanchfield believes that “Industry40 is only possible where high speed trusted secure low latency high data throughput networks like 5G as data is the catalyst for smart manufacturing.
Maryson W. states that the litmus test is on. If we want AI to someday manage everything, the time to act is now. When factories would be less manually monitored in terms of immovable assets, 5G could open doors to 4K security cameras. He agrees with me that 5G sums up as a backbone for IoT, IIoT devices and easing up digital twin operations.
My POV: Advanced wireless technologies like 5G, edge, or Wi-Fi can maximize flexibility in connecting data collection end points. Advanced internet solutions such as business fiber, create the backbone on which to build advanced wireless technologies at speeds needed for real-time decisioning.
Dez Blanchfield: The key here is that one is wireless (5G) and the other is a “fixed wire” (fiber) technology, they serve very different yet powerful and valuable solutions to manufacturing sites.
My POV: It all begins with business priorities. What business outcome you are trying to achieve, followed by technologies needed to enable it, then you can determine what expertise you need. A few areas of priorities I have seen are AI, ML, IoT, Big Data and Analytics. Choosing the right partner with required expertise is critical.
Dez Blanchfield: Successful smart manufacturing businesses are choosing partners of choice to design, deploy and manage networks of the future for them while they focus on their core business.
Maryson W. believes that “the probability of not requiring blockchain is under 50%.
My POV: Network security plays a critical role in the digital revolution for manufacturing. As manufacturing facilities increasingly adopt IIoT devices, automation systems, and cloud computing, the attack surface for cyber threats also expands. Network security measures are critical to safeguard the digital assets. Implementing firewalls, intrusion detection and prevention systems, access control mechanisms, and encryption protocols to prevent unauthorized access, data breaches and other cyberthreats. Network security in manufacturing is also involved in securing the supply chain, as many manufactures rely on 3rd party vendors for components and services.
Dez Blanchfield: Security or cybersecurity in today’s language, has always played a mission critical role in the evolution of manufacturing, now it is a key element of the digital revolution.
My POV: The biggest barrier to network security is lack of awareness and expertise and the increasing complexity of the manufacturing network, with the adoption of more digital technologies and the interconnectivity of various devices and systems. Manufacturers may prioritize meeting their production goals over security due to perceived costs or lack understanding of the potential risks. In addition, the increasing frequency and sophistication of cyberattacks pose a significant challenge to network security and reliability.
Dez Blanchfield: Often an early barrier to digital transformation is education or awareness, along with smart design and implementation of the right tools and systems to enable them.
My POV: A7. MEC is multi-access edge computing, a managed service that enables enterprise customers to differentiate and route specific data traffic to designated customer applications in a private wireless network campus environment based on device, IP address, and customer policy. It allows factories to put decision-making intelligence within this edge computer, and that edge computer then can decide what can be on my network and what can’t be on my network. It puts an inherent security capability on top. It's a piece of equipment that makes intelligent decisions within the factory.
It brings edge computing closer to the manufacturer vs the network edge from the cloud provider network edge. It takes the cloud network edge right into your facility. It reduces complexity because it makes a distributed decision about what to keep and not to keep.
Dez Blanchfield: MEC has proven to be a massively powerful enabler of digital technologies and telecommunications and data analysis and insights in manufacturing.
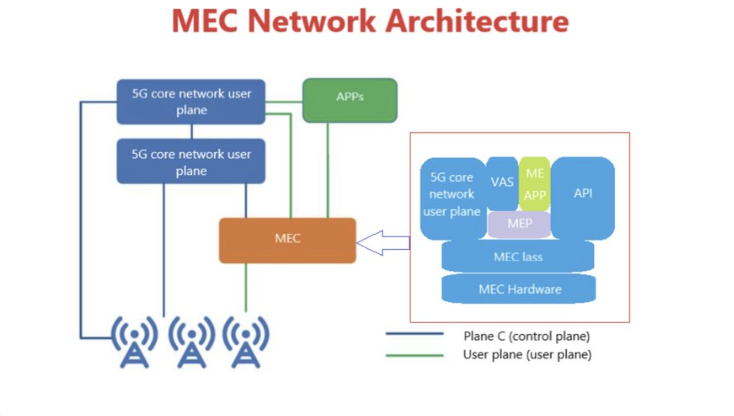
Maryson W.: Mobile edge computing or MEC is helpful in aligning a smart factory to the cloud, and certainly calls for networks which have self-recovering capabilities given the numerous doors of automation technologies at disposal.
I walked away from the #BizTalks more inspired and excited about the future of smart factory.
The smart factory of the future requires secure networking and reliable connectivity. This includes security at the device level, network level, edge and cloud. These overlapping layers of protection provided by AT&T help reduce risk and identify threats when they emerge:
● Cybersecurity strategy, planning and assessment services.
● DDoS defense and application layer security
● Managed firewall services
● AT&T Global Security Gateway
● Cloud security strategy and assessment
● Threat detection and response solutions
The complex nature of a modern security environment requires experts in cybersecurity — managed security services are easier than training or hiring an in-house expert. Choose a vendor with a trusted history of enterprise-level service.
As we continue to embrace the evolution of smart manufacturing, it’s crucial to prioritize security and connectivity to ensure a successful future. With AT&T’s expertise in cybersecurity and reliable networking, smart factories can operate efficiently, sustainably, and securely. Let’s strive towards a future where data-driven insights and technology advancements drive innovation and success. Thank you for joining us on this journey towards the smart factory of the future.
Follow #BizTalks on Twitter to learn more.
Helen Yu is a Global Top 20 thought leader in 10 categories, including digital transformation, artificial intelligence, cloud computing, cybersecurity, internet of things and marketing. She is a Board Director, Fortune 500 Advisor, WSJ Best Selling & Award Winning Author, Keynote Speaker, Top 50 Women in Tech and IBM Top 10 Global Thought Leader in Digital Transformation. She is also the Founder & CEO of Tigon Advisory, a CXO-as-a-Service growth accelerator, which multiplies growth opportunities from startups to large enterprises. Helen collaborated with prestigious organizations including Intel, VMware, Salesforce, Cisco, Qualcomm, AT&T, IBM, Microsoft and Vodafone. She is also the author of Ascend Your Start-Up.
Leave your comments
Post comment as a guest